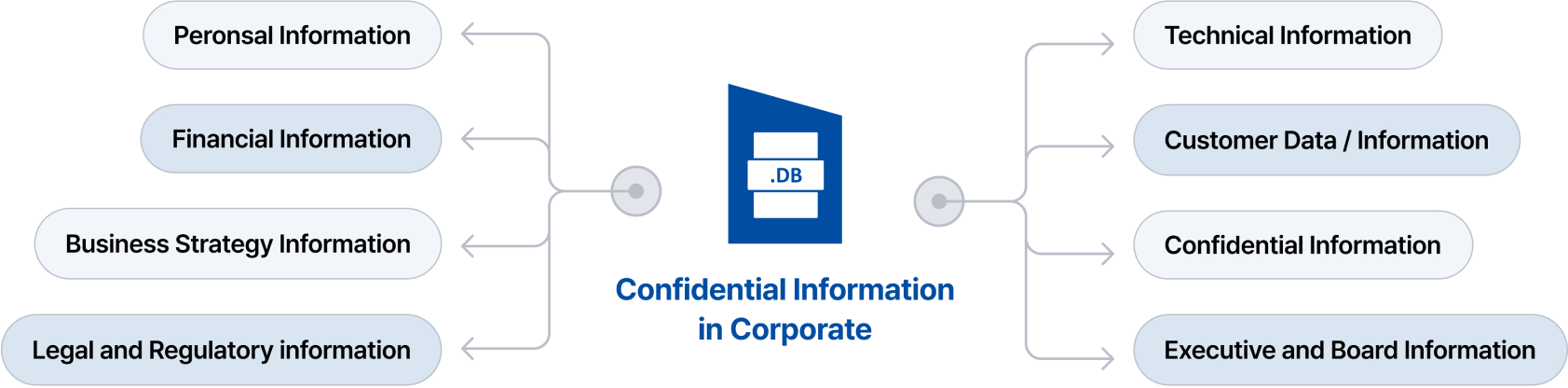
What Is Confidential Data within an Organization?
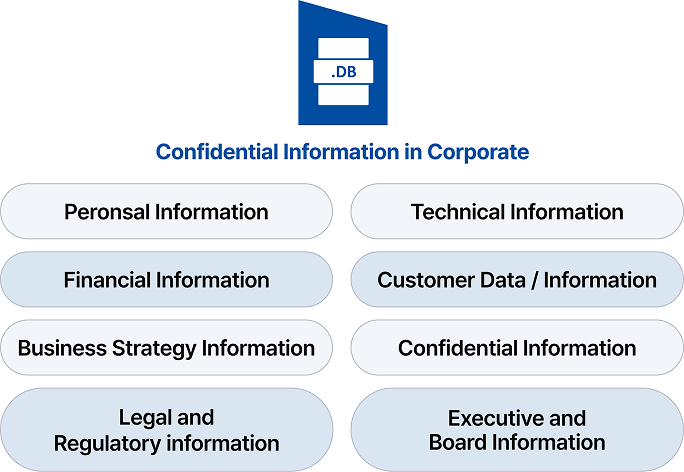
Confidential data within an organization refers to information that is accessible only to individuals with specific access and is generally highly sensitive, thus requiring information security. Due to the sensitivity of this information, access permissions are strictly controlled according to the company's policies, ensuring that only authorized individuals can access it. Security measures are implemented alongside this to safeguard the information.
So, how are different types of confidential data actually protected within organizations?
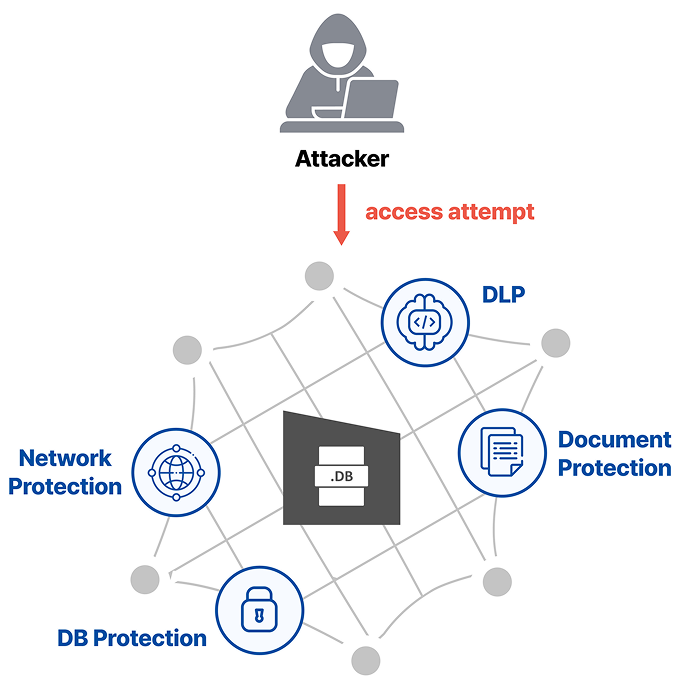
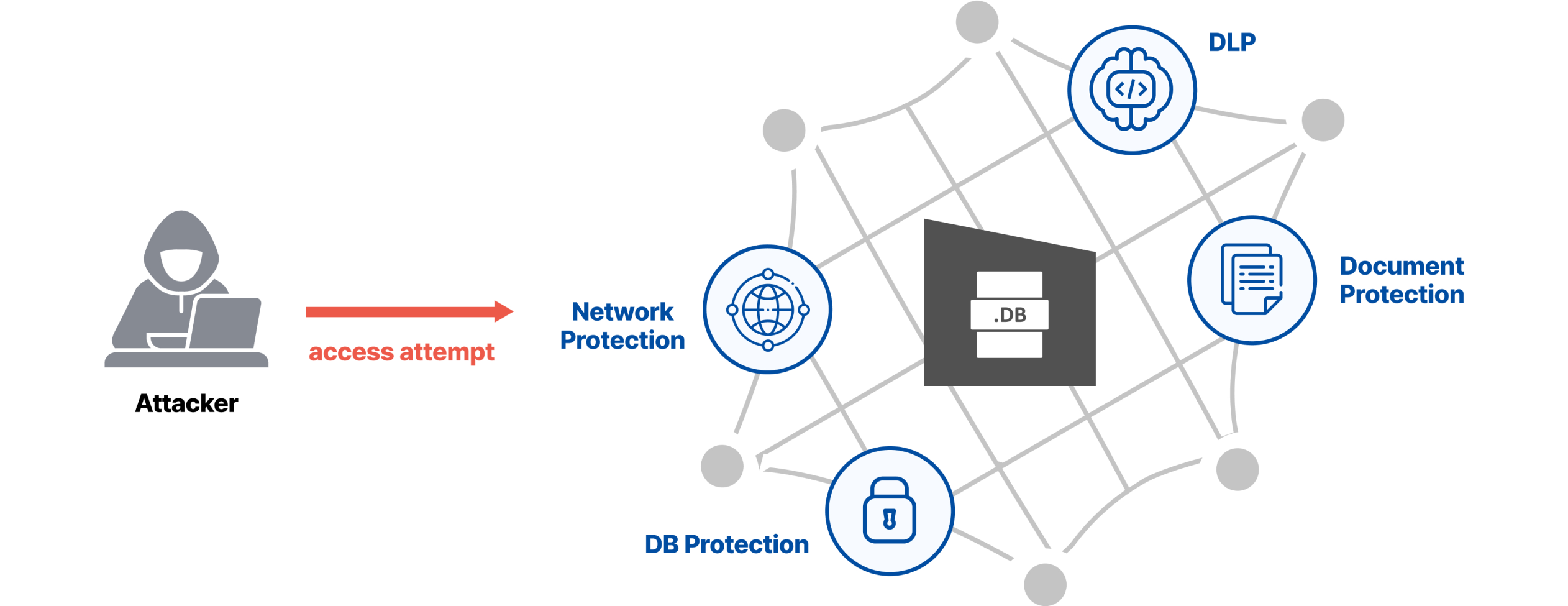
Most companies implement multiple solutions to protect internal information. From network security to prevent unauthorized access, database security, document security to prevent information leakage in document form, and DLP(Data Loss Prevention) to prevent data leakage through various channels, a comprehensive security framework is applied. These layers of protection create a tight security net that helps safeguard sensitive information across different levels and touchpoints.
How is the Security System for Data Protection Built?
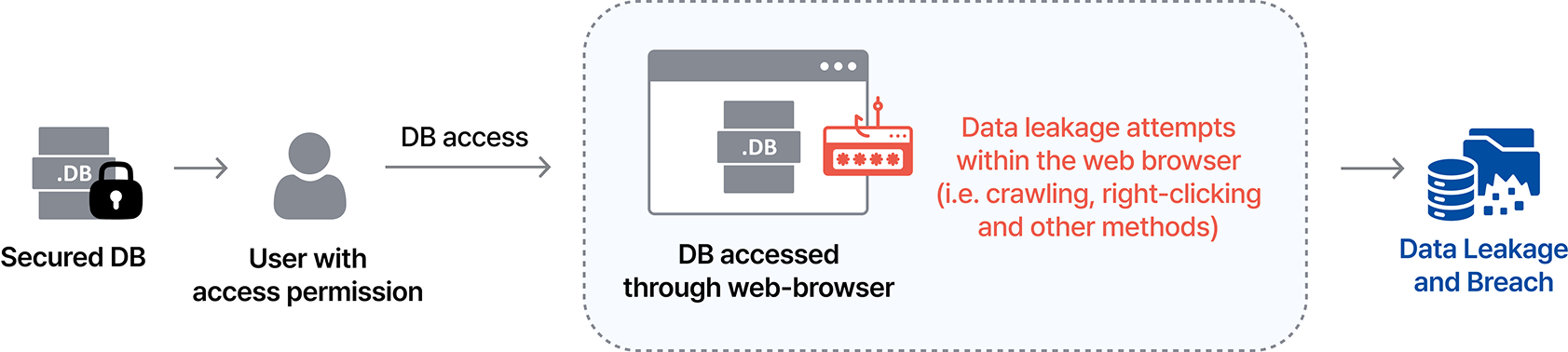
For document access, security systems typically prevent data duplication and leakage while still allowing the use of existing viewer applications within document DRM. On the other hand, for non-document data accessed within the organization, the system can be provided as a web service instead of a traditional installed program. Initially, installed programs were strongly preferred due to their user interface and security advantages. However, these systems face challenges such as frequent compatibility issues across different operating systems and versions, as well as high development and maintenance costs.
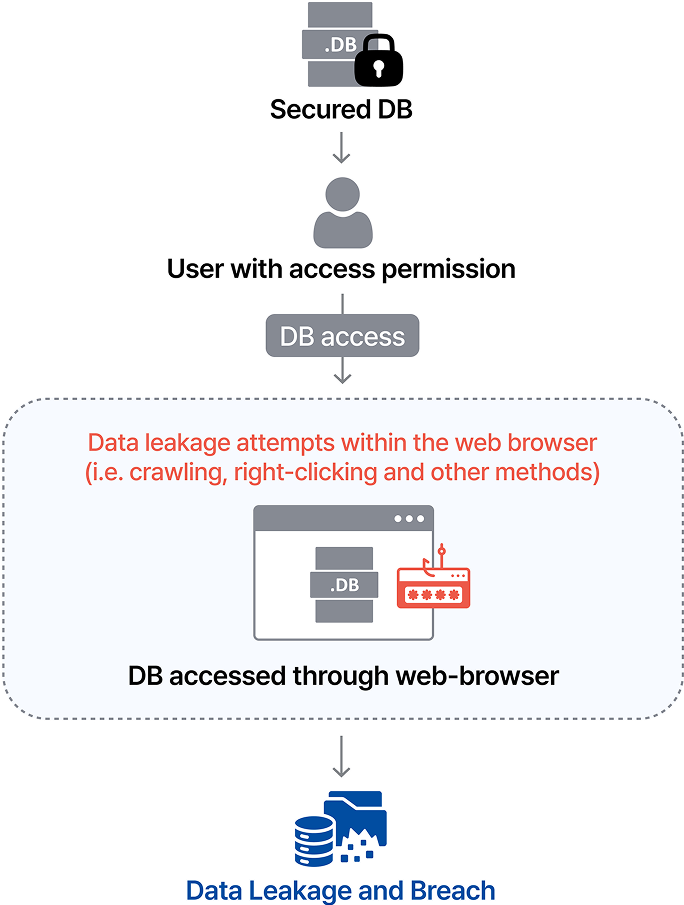
For these reasons, companies today prefer web-based systems, which are significantly more cost-effective to develop and maintain. Despite these benefits, the adoption of web-based systems within organizations is still under discussion due to concerns over data leakage and security vulnerabilities. The primary issue is that preventing unauthorized duplication or leakage of data through web browsers is difficult. As discussed in the illegal webtoon market post, there are numerous ways to duplicate content, and implementing protective measures against all of them is challenging.
There are many bypass methods for unauthorized data extraction, such as using scripts to automatically crawl specific sites and collect data, utilizing the browser's "Save" (Ctrl+S) function, right-click downloading, or manual copying. Even if data is stored in a strongly encrypted database and access is restricted to specific users, once the data is displayed in a web browser, it can be easily duplicated through various browser-based copying methods.
Therefore, security measures on the web browser are essential.
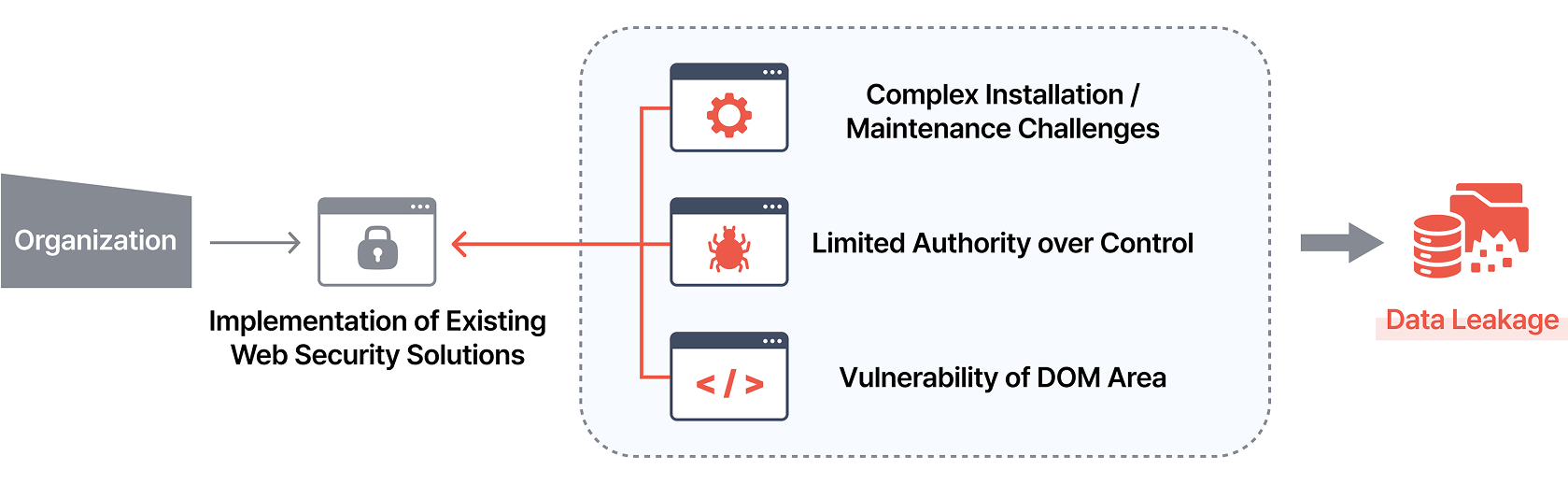
Companies are actively exploring various ways to enhance web security, and screen capture prevention is one of the most widely adopted solutions. This technology blocks screen capture attempts and restricts the use of debugging tools. However, despite these measures, certain challenges remain.
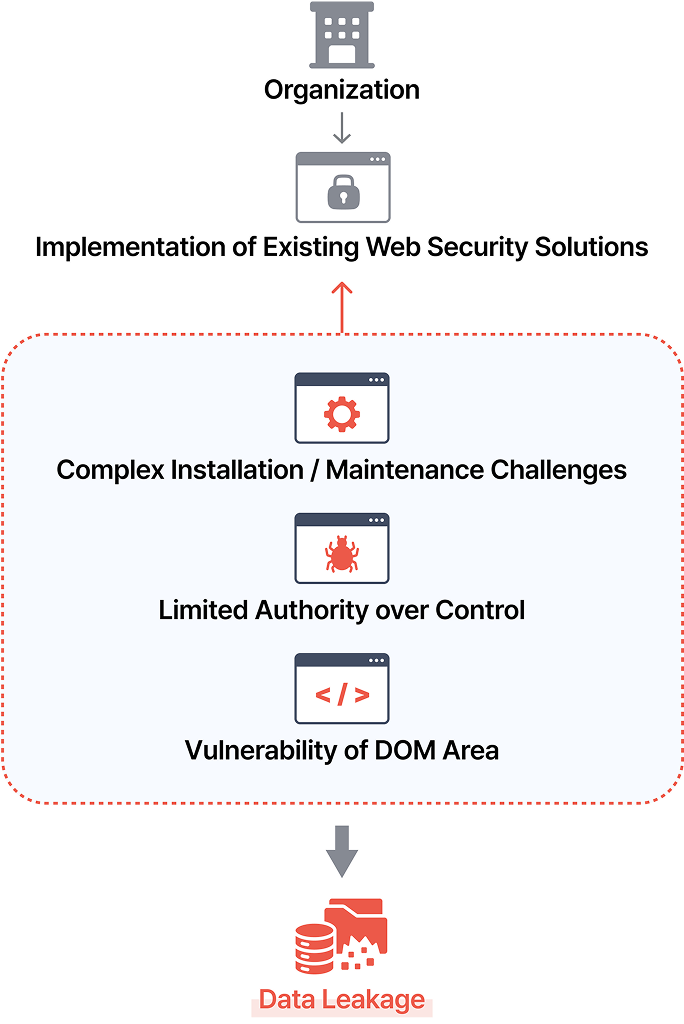
The issues can be broadly categorized into three main points.
1. Complex Installation and Maintenance Challenges
Most existing web security solutions, such as screen capture prevention, often require additional installations, like client-side setups. This makes maintenance across different operating systems challenging and complicates keeping up with updates. As a result, the goal of reducing maintenance costs compared to applications does not align with the shift to web-based services.
2. Limited Authority over Control
Most existing web security solutions, such as screen capture prevention, often require additional installations, like client-side setups. This makes maintenance across different operating systems challenging and complicates keeping up with updates. As a result, the goal of reducing maintenance costs compared to applications does not align with the shift to web-based services.
3. Vulnerability of DOM Area
Data within the web browser’s DOM area exists in plaintext format, making it visible on the screen. Therefore, access to it must be entirely prevented. Even with strong security measures in place to block access to the DOM area, once an authorized user gains access, data extraction becomes possible. To mitigate this risk, both security measures for the DOM area and data-level protection are necessary. However, solutions that require installing additional programs, such as screen capture prevention tools, only restrict browser functionalities at the application level and do not provide the encryption or decryption capabilities needed to secure internal DOM data.
So, How Can We Securely Protect a System Accessed via a Web Browser?
The answer lies in implementing preemptive security measures on the web browser. Let’s explore Web-X DRM, a web browser security solution.
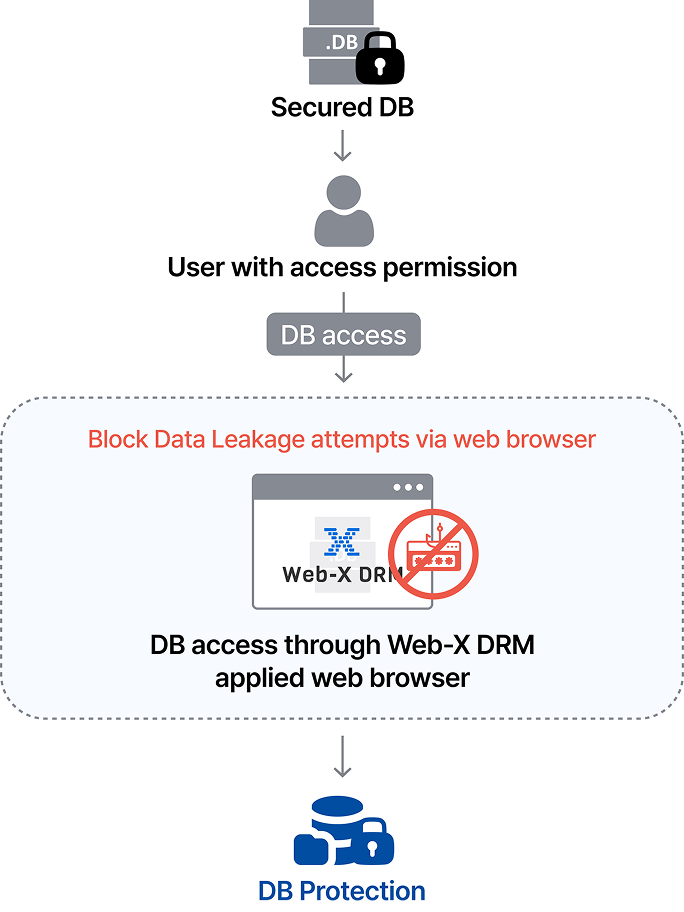
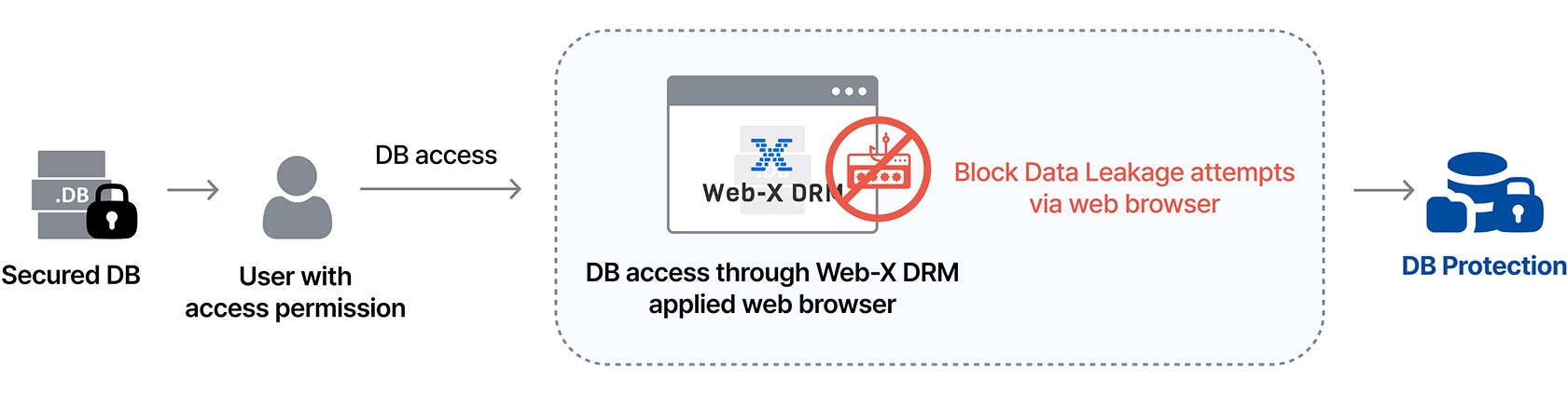
Earlier, we discussed how encrypted and access-controlled database (DB) data can still be easily copied illegally when viewed through a web browser by an authorized user. By applying Web-X DRM to the web browser, authorized users can continue accessing the information as intended while preventing unauthorized duplication.
However, the Web-X DRM solution provides fundamental protection by incorporating features such as text obfuscation, image source hiding, developer tool execution prevention, print control, copy/paste prevention, crawling prevention, screen capture prevention, and visible/invisible watermarking. These measures take effect as soon as the user views the page, effectively preventing unauthorized duplication and blocking browser-based copying.
As more systems transition from applications to web-based formats, implementing preventive measures to secure sensitive company data before any unauthorized leakage occurs becomes increasingly critical. This proactive approach is essential for safeguarding valuable information within any organization.
With the right protection measures in place, organizations can protect their valuable data and stay ahead of potential threats. With Web-X DRM, take the next step toward stronger security and build a safer digital system.
List